Did you know that by default, you can check in code as anyone in your git repository? All you need to do is run git config.username = {username} and git config.email={email} and you can trick git into thinking you are someone else.
To better understand what kinds of problems this can create, go and read Mike Gerwitz’s article, A Git Horror Story.
Luckily, Git allows you to resolve this issue pretty easily - by letting you sign commits using GPG(GNU Privacy Guard).
The GitHub help article Signing commits using GPG is a pretty good guide on how to set it up. But, it requires you to use the git bash console.
So, what do you do if you are on a Windows machine and would prefer to use a GUI like me? Don't fear. This guide will tell you what you need to know.
Using Gpg4win with Git needs a little bit of configuration so let's start configuring it.
Setup Kleopatra
- Download Gpg4win and install it using the installer.
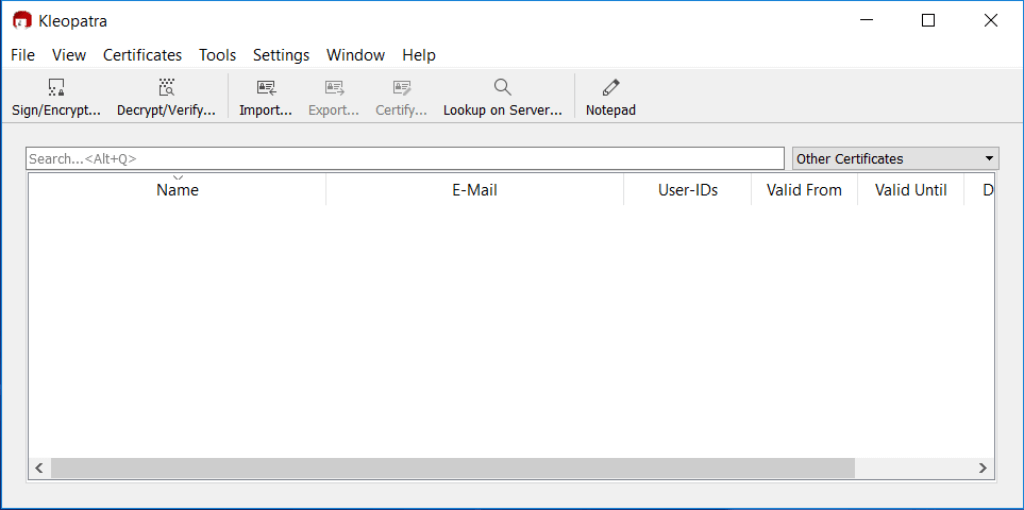
- Go to the Start menu and start Kleopatra
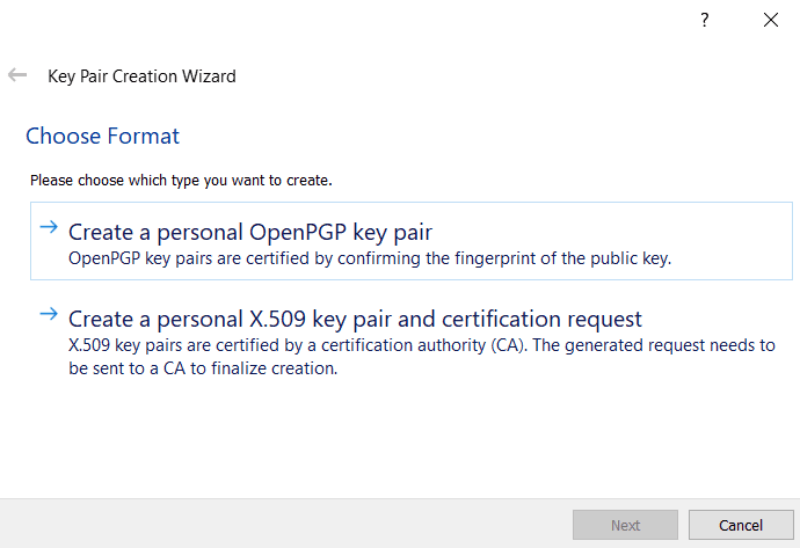
- Click on File -> New Key Pair
- Click on Create a Personal OpenPGP key pair
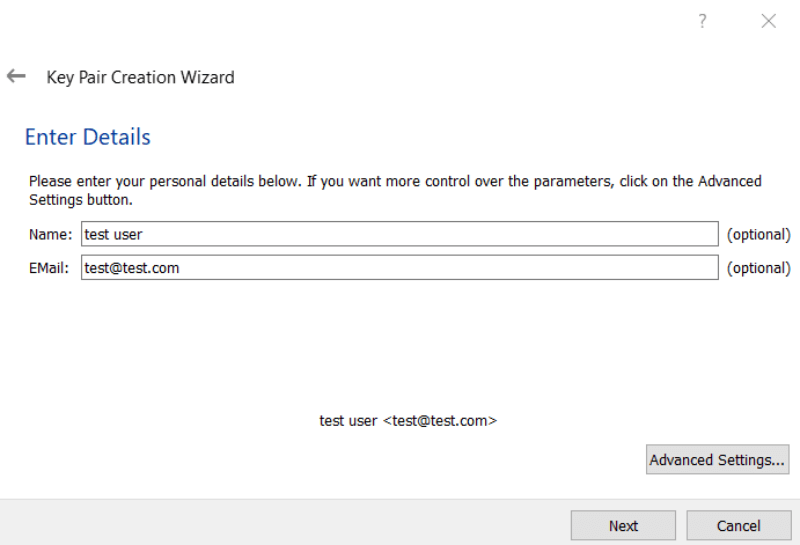
- Enter details and click next.
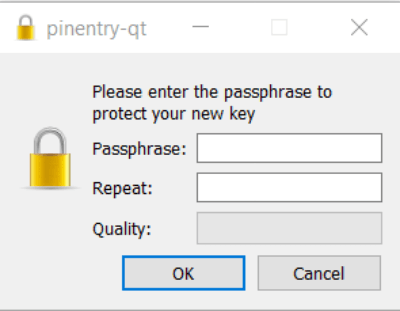
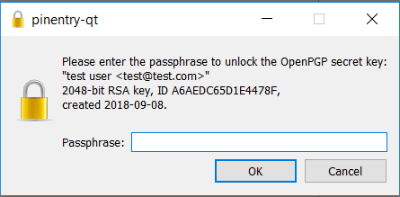
- Review and Create the key. This will show a popup asking you to enter a passphrase to protect the key.
- Enter a passphrase and click Ok
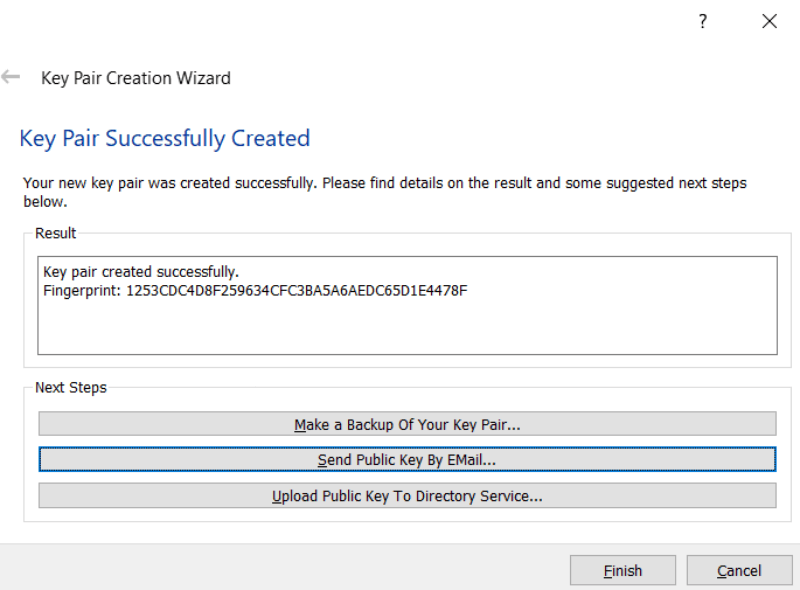
- At this point, the key pair should be created. Click on Finish.
You can create a backup of the key and save it somewhere safe.
- You should now see the key in Kleopatra
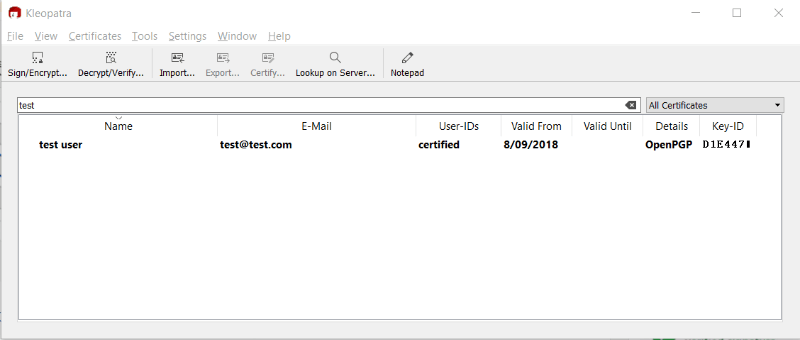
- Keep a note of the Key-ID. We will need it in a minute.
This is D1E4471 in the screenshot above.
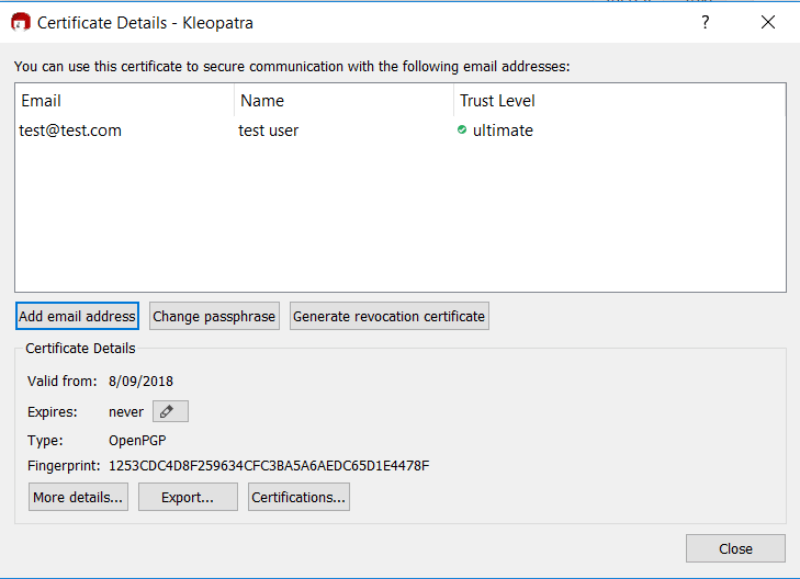
- Double click the key to see the certificate details
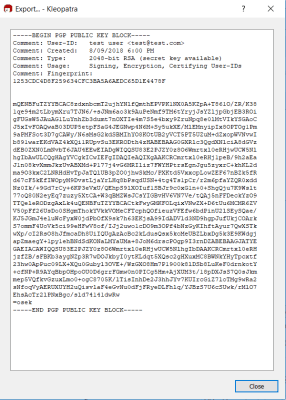
- Click on export and copy the public gpg key.
Make sure you copy everything including -----BEGIN PGP PUBLIC KEY BLOCK----- and -----END PGP PUBLIC KEY BLOCK-----
Configure Git to Sign Commits
Update the global git config to use the signing key. Remember the Key-ID from above - You will need it here.
Enter
git config user.signingkey D1E4471in your git consoleIf you want to set it on a global level, use
git config --global user.signingkey D1E4471insteadInstruct git to sign every commit automatically.
Enter
git config commit.gpgsign truein your git console. If you want to set it on a global level, usegit config --global commit.gpgsign trueinstead.Instruct git to sign every tag automatically.
Enter
git config tag.gpgsign truein your git console. If you want to set it on a global level, usegit config --global tag.gpgsign trueinsteadTell git to use the gpg4win version of gpg.exe
Enter
git config --global gpg.program "C:\Program Files (x86)\GnuPG\bin\gpg.exe"in your git console.
You might need to tweak the location of the program if you installed it in a custom location.
To check that it works, commit some code to a repository that has been set up to use signing. You should be prompted for the passphrase you entered earlier.
Configure Kleopatra to cache the passphrase for a longer time
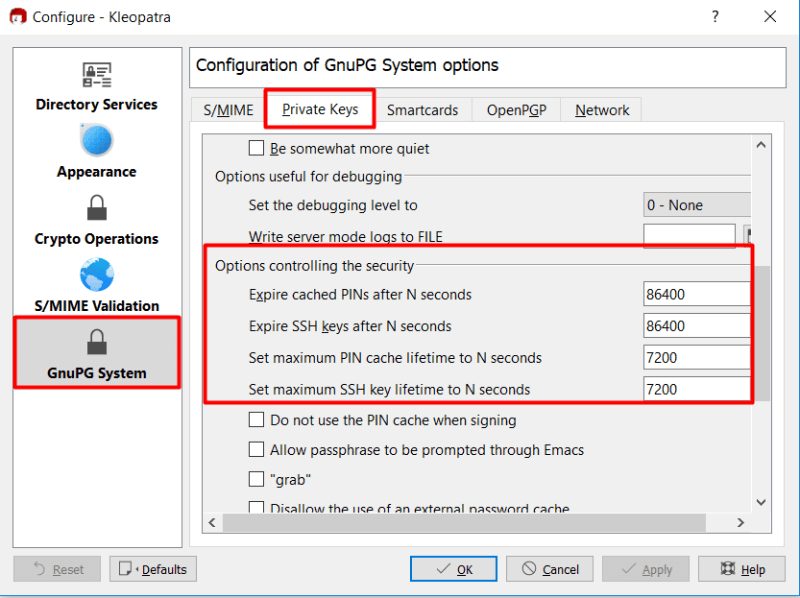
- Run Kleopatra. Click on Settings -> Configure Kleopatra
- On the configure page, click on GnuPG System -> Private Keys and scroll down to the Options controlling the security section.
- Set the cache time. 86400 seconds is equal to 1 day.
Configure Github to show verified commits
- Follow the steps at Adding a new GPG key to your GitHub account so that Github can show the verified commits. Use the public gpg key that you had copied earlier.
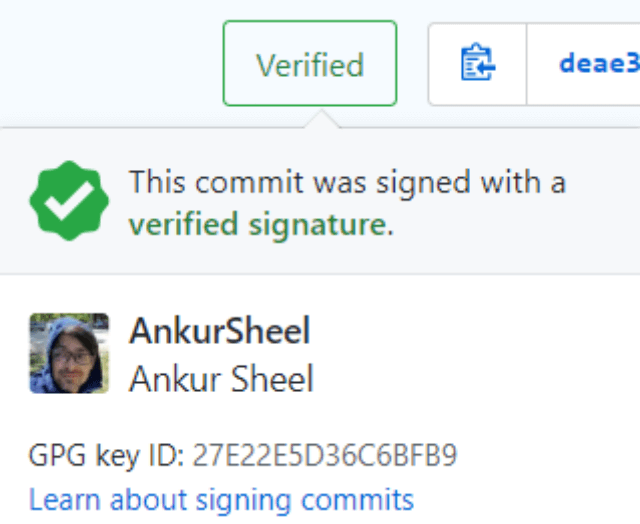
To check if it works, push the signed commit. You should see the Verified tag in the commit history on Github.
The commit should have a verified tag which you can click to see additional details.
Conclusion
Now all the commits will have a verified tag. Do you sign your commits? Let me know